通过SSH服务第一次登录到服务器上的客户端IP地址为?(标准格式:192.168.1.1)

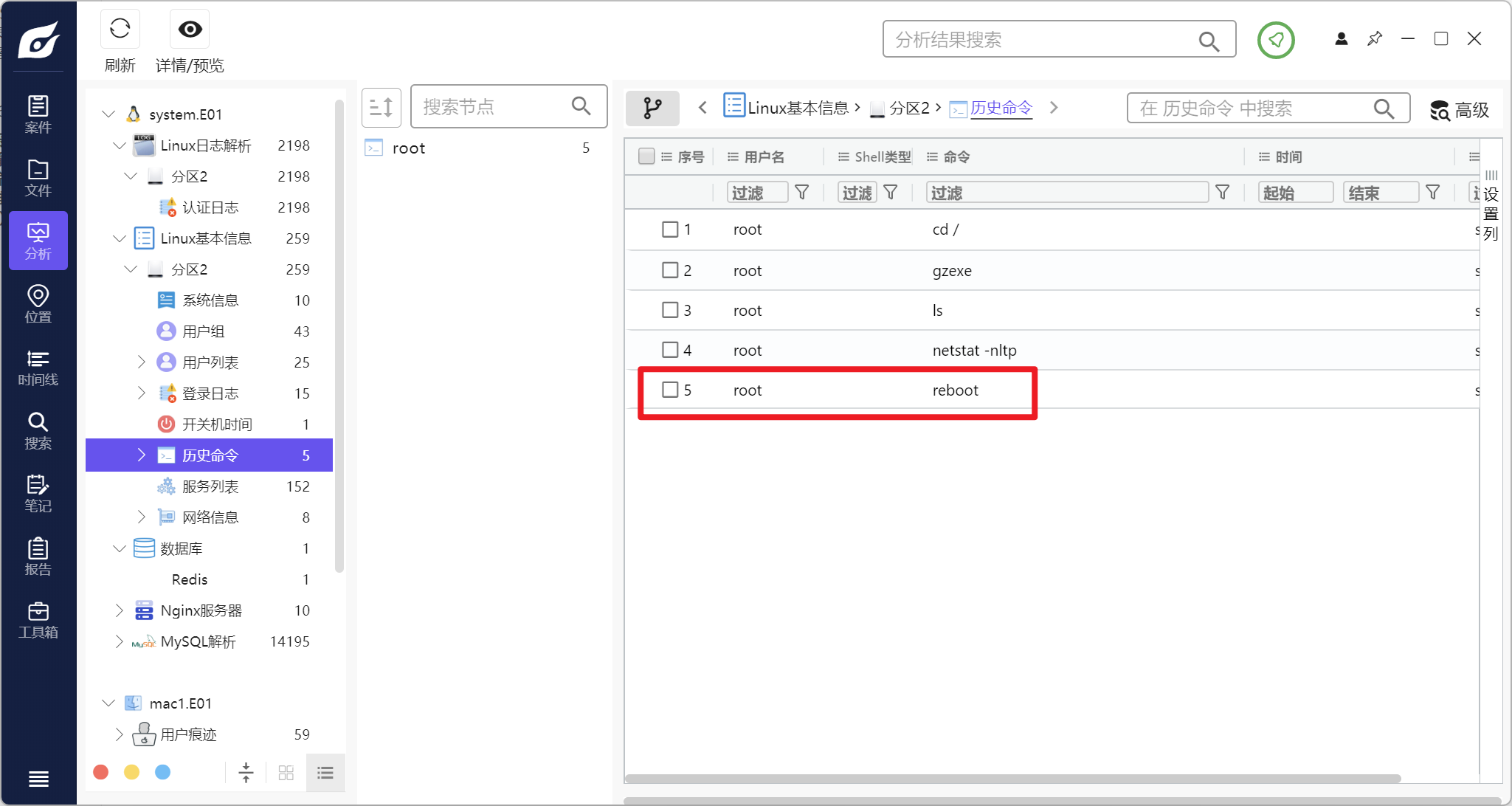
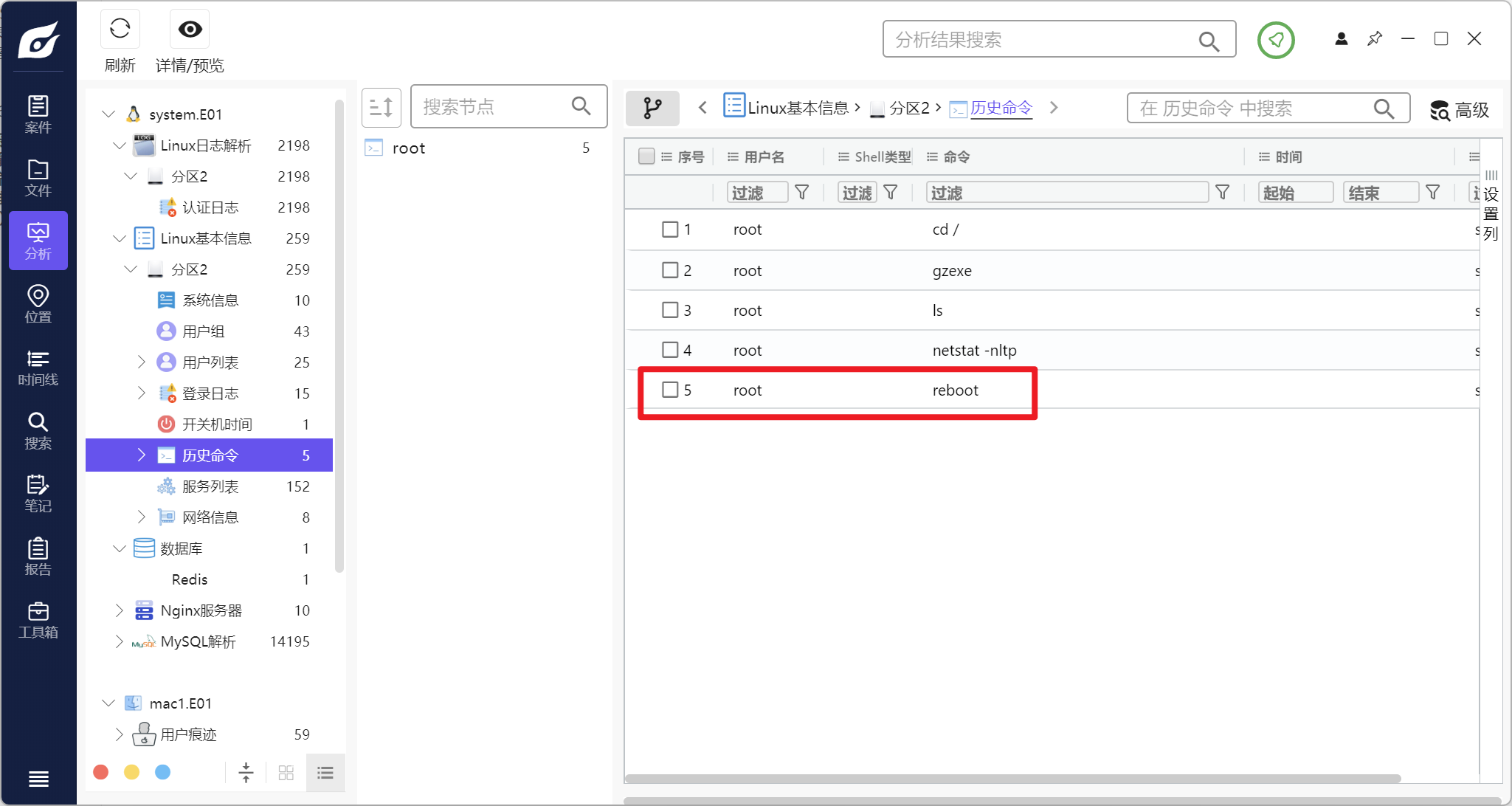
分析服务器ROOT用户输入的最后一条命令为?(标准格式:good)
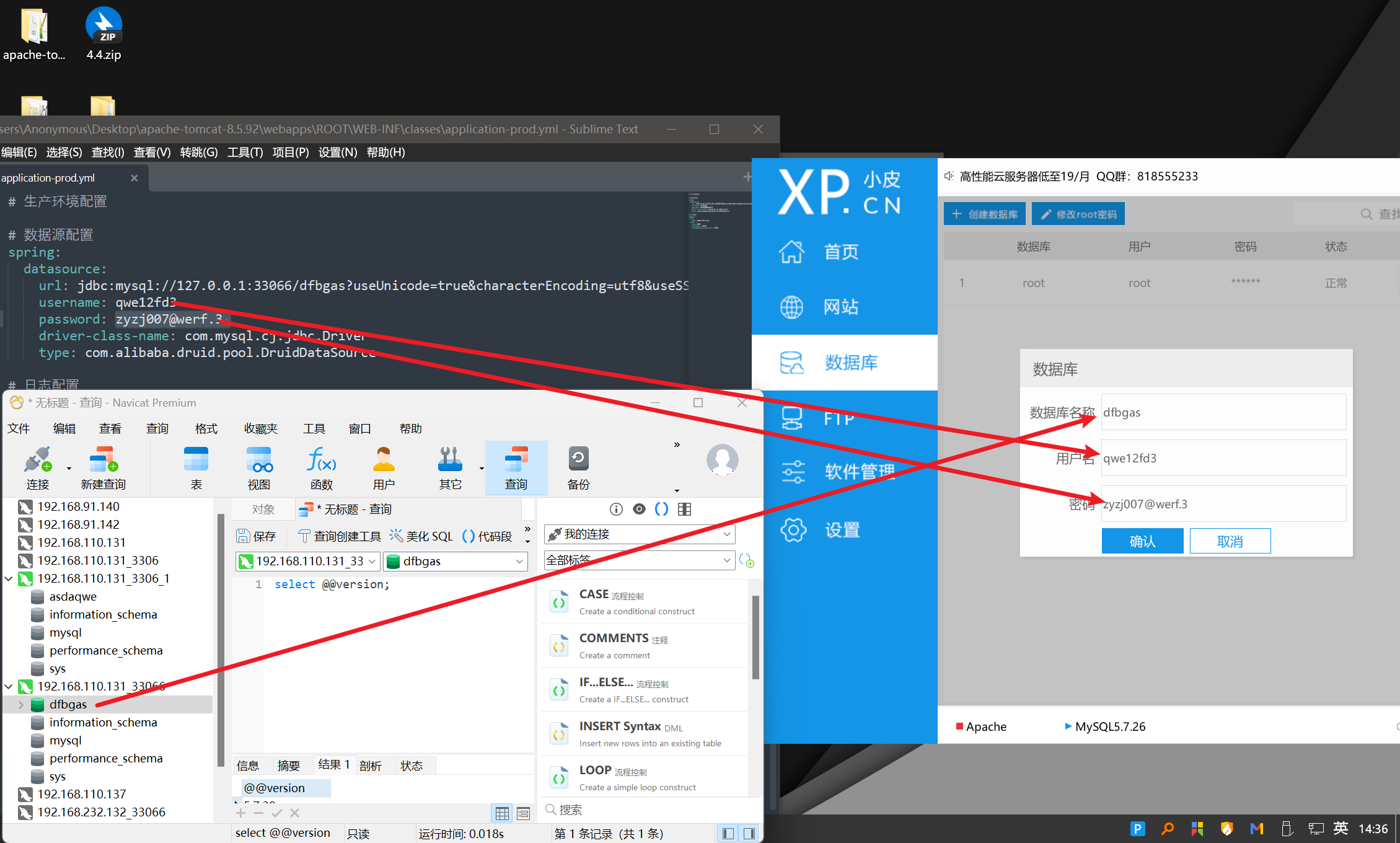
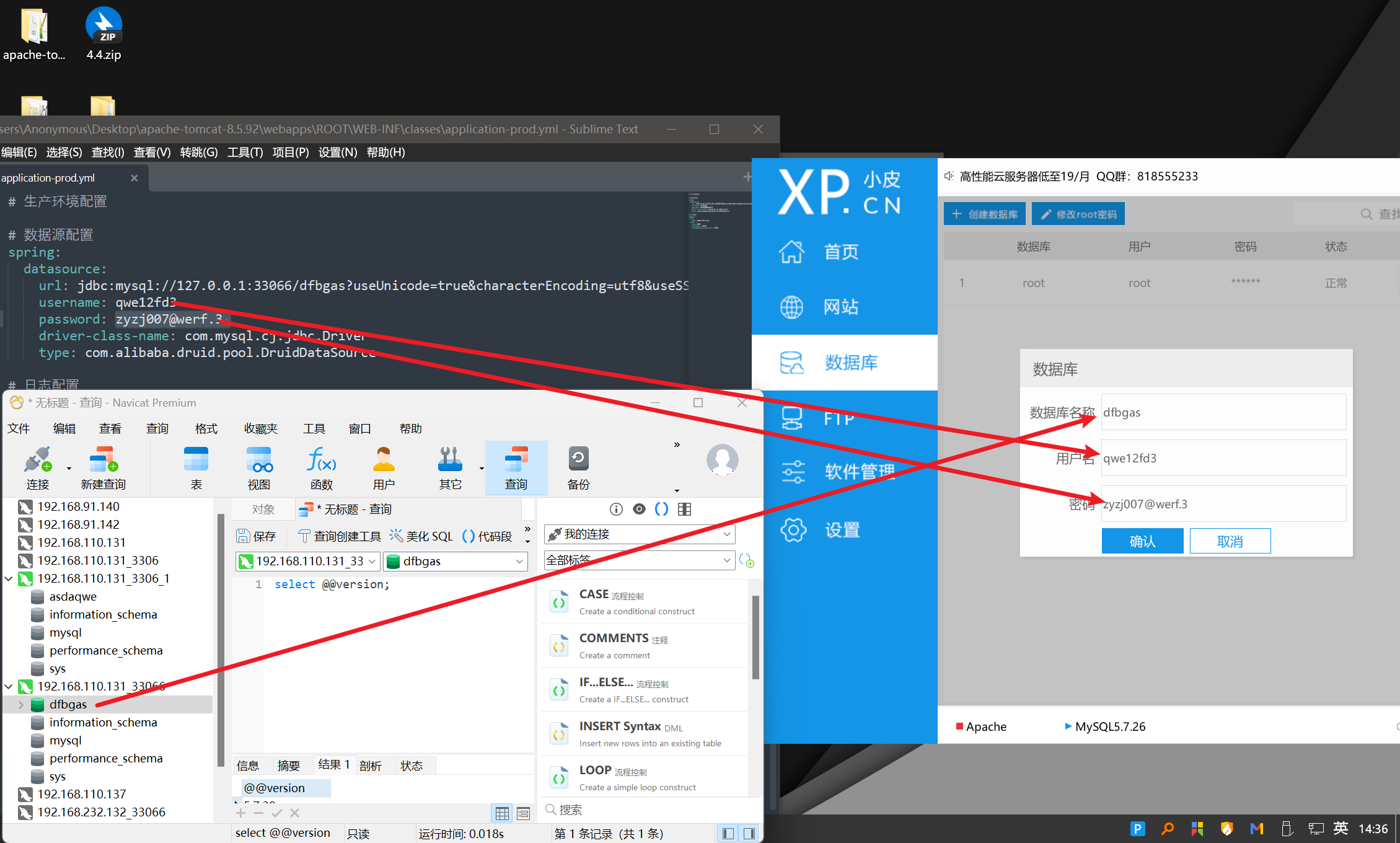
分析虚假发卡网站源码中配置的数据库用户名为?(标准格式:good)
下面开始对服务器进行分析
服务器仿真后,我会用这几个命令大致排查一下
1
2
3
4
5
6
| ifconfig
history
netstat -nlpt
crontab -l
cat /etc/crontab
cat /etc/rc.d/rc.local
|

本题中初次仿真服务器,历史命令是很干净的,合理怀疑有定时任务或者开启自启项

发现了一个定时任务

一眼gzexe加密过了
Shell脚本加密与解密-腾讯云开发者社区-腾讯云 (tencent.com)

三句话,分别是,清空历史记录,清空kkk网站的日志,清空shop网站的日志
再看端口开放情况

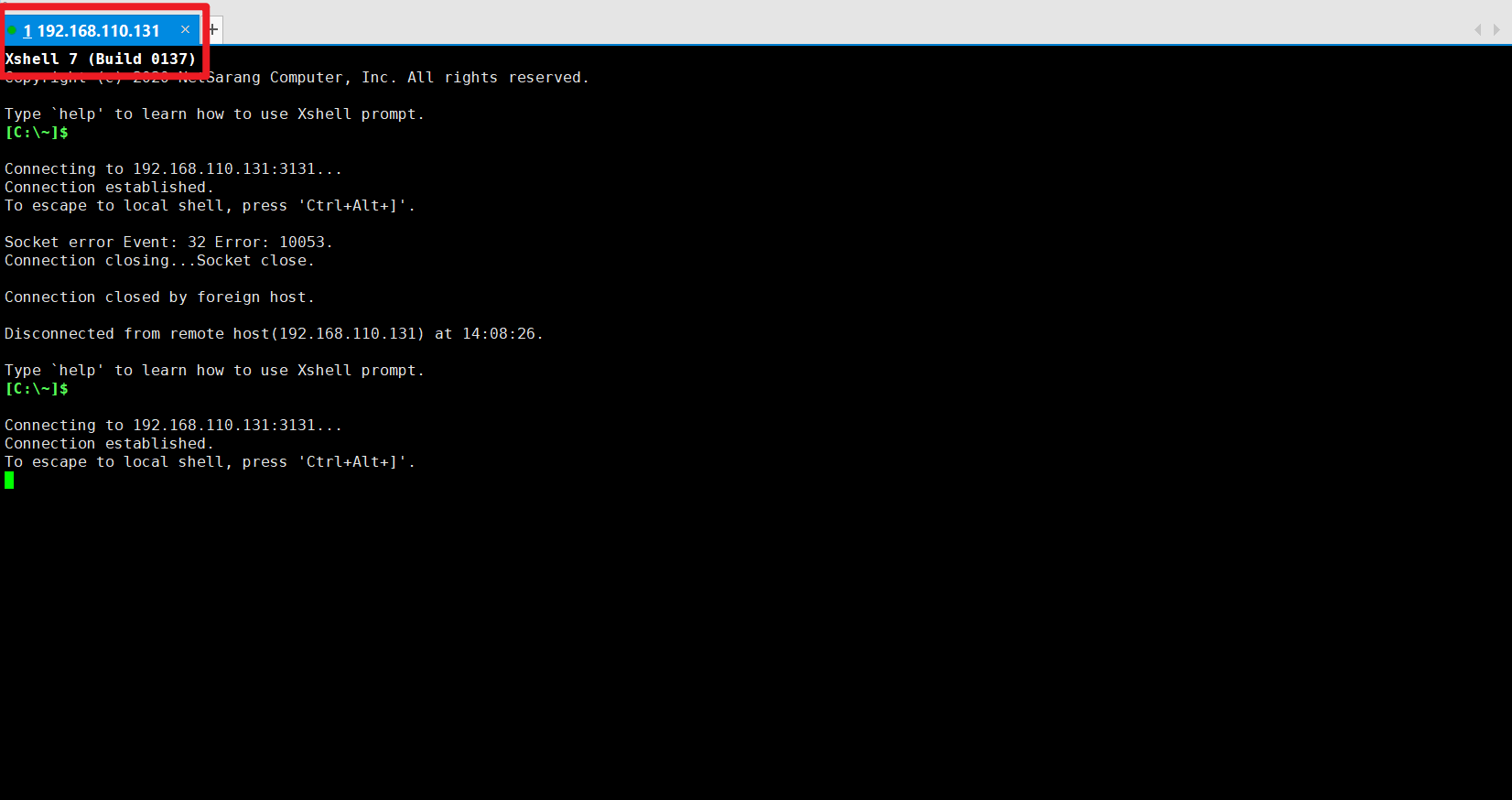
开放了ssh端口3131,尝试连接
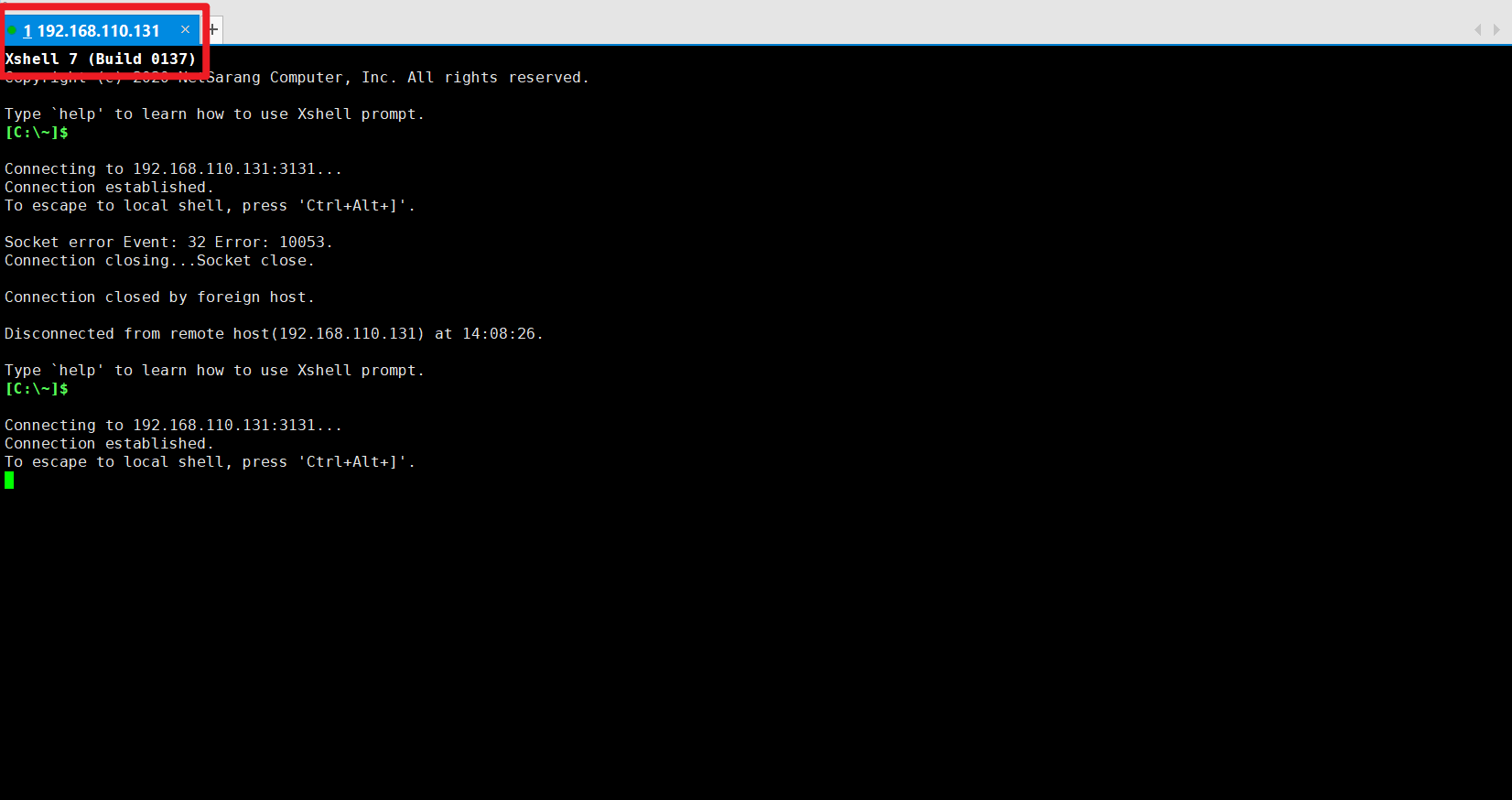
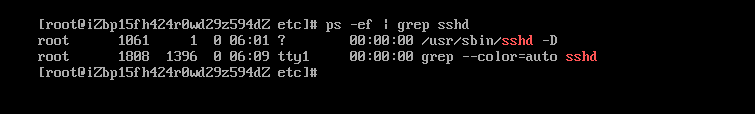
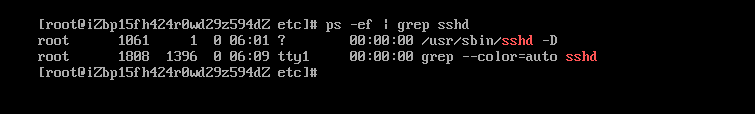
端口是正常开放,服务也正常开启的,但就是连不上
SSH之hosts.allow和hosts.deny文件-腾讯云开发者社区-腾讯云 (tencent.com)
排查这两个文件

限制ip访问ssh服务了,把这两个文件删掉,重启

成功连接
接下来观察data.E01挂载在哪里了

重点查看data目录



一个tomcat站,一个php站,排查他们的配置文件
/data/kkkfffasda1.com/config/database.php
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
| <?php
return [
'debug' => false,
'fields_strict' => true,
'auto_timestamp' => false,
'sql_explain' => false,
'type' => 'mysql',
'hostname' => '118.31.4.104',
'database' => 'asdaqwe',
'username' => 'fefjisd',
'password' => 'zyzj008asd',
'hostport' => '3306',
'prefix' => '',
'charset' => 'utf8',
'params' => [],
];
|
/data/shop.zzpay.com/WEB-INF/classes/application-prod.yml
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
|
spring:
datasource:
url: jdbc:mysql://118.31.4.104:33066/dfbgas?useUnicode=true&characterEncoding=utf8&useSSL=false&serverTimezone=GMT%2B8&rewriteBatchedStatements=true
username: qwe12fd3
password: [email protected]
driver-class-name: com.mysql.cj.jdbc.Driver
type: com.alibaba.druid.pool.DruidDataSource
logging:
file:
name: bomao-faka.log
level:
root: WARN
com.bomaos: ERROR
com.baomidou.mybatisplus: ERROR
|
Q:4个yml文件,什么就看application-prod.yml呢?

A:dev表示当前加载测试环境配置application-dev.yml
prod表示加载生产环境的配置文件application-prod.yml
test表示加载测试环境的配置文件application-test.yml
application.yml没有具体内容,所以忽略

服务器中还有docker服务,看名字应该是与网站相连接的数据库

端口都跟配置文件里对上了,应该没问题,到这步其实网站已经可以本地重构了
我们把网站源码和数据库down下来

导出sql文件

数据库版本都一样,所以放在同一个数据库没问题
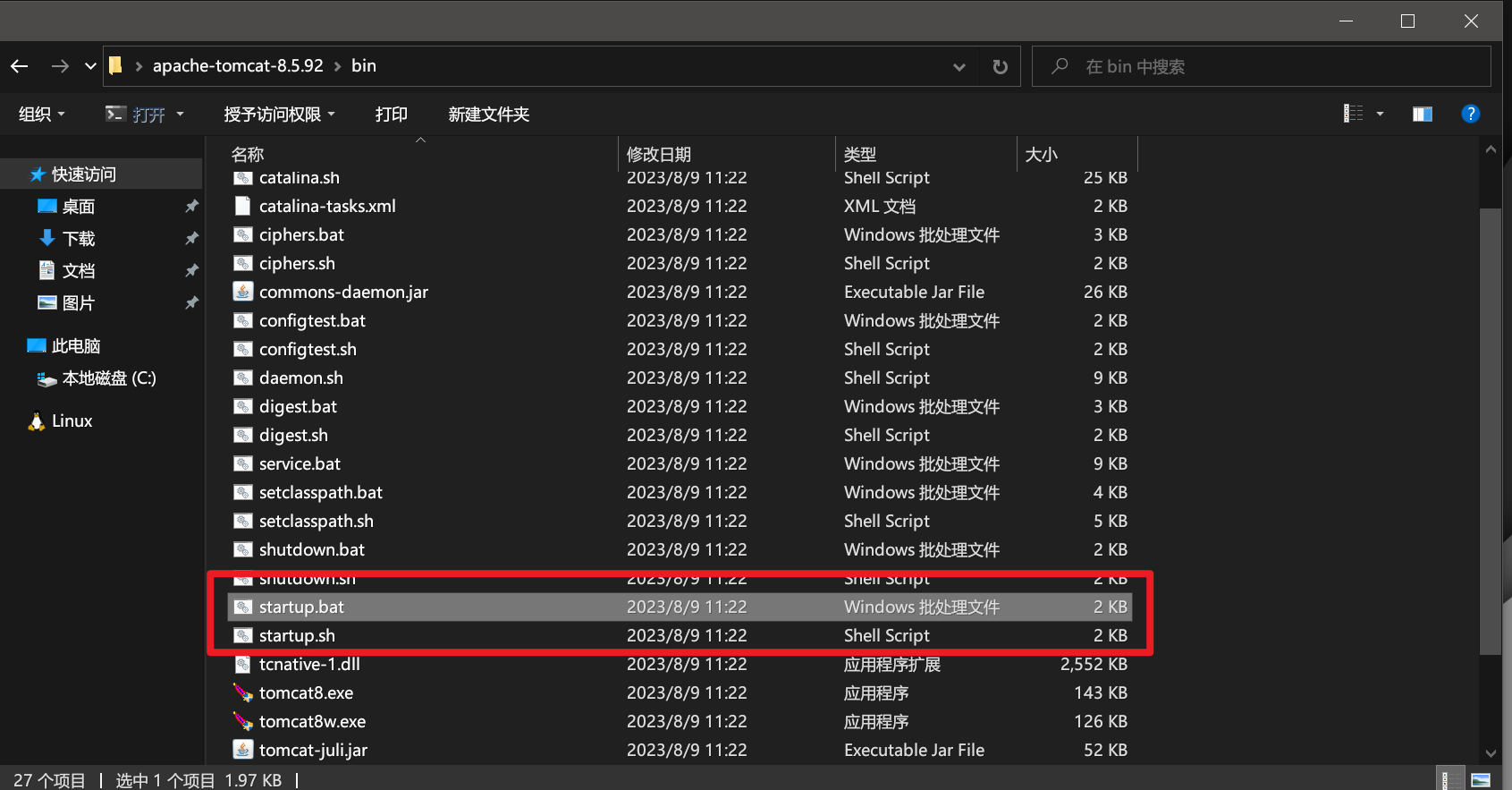
本地:网站源码,sql文件,tomcat,phpstudy

将tomcat webapps里的ROOT目录替换,yml里的ip都指向本地


最后双击start.bat
tomcat启动:startup.sh、catalina.sh、setclasspath.sh三者关系 - 简书 (jianshu.com)
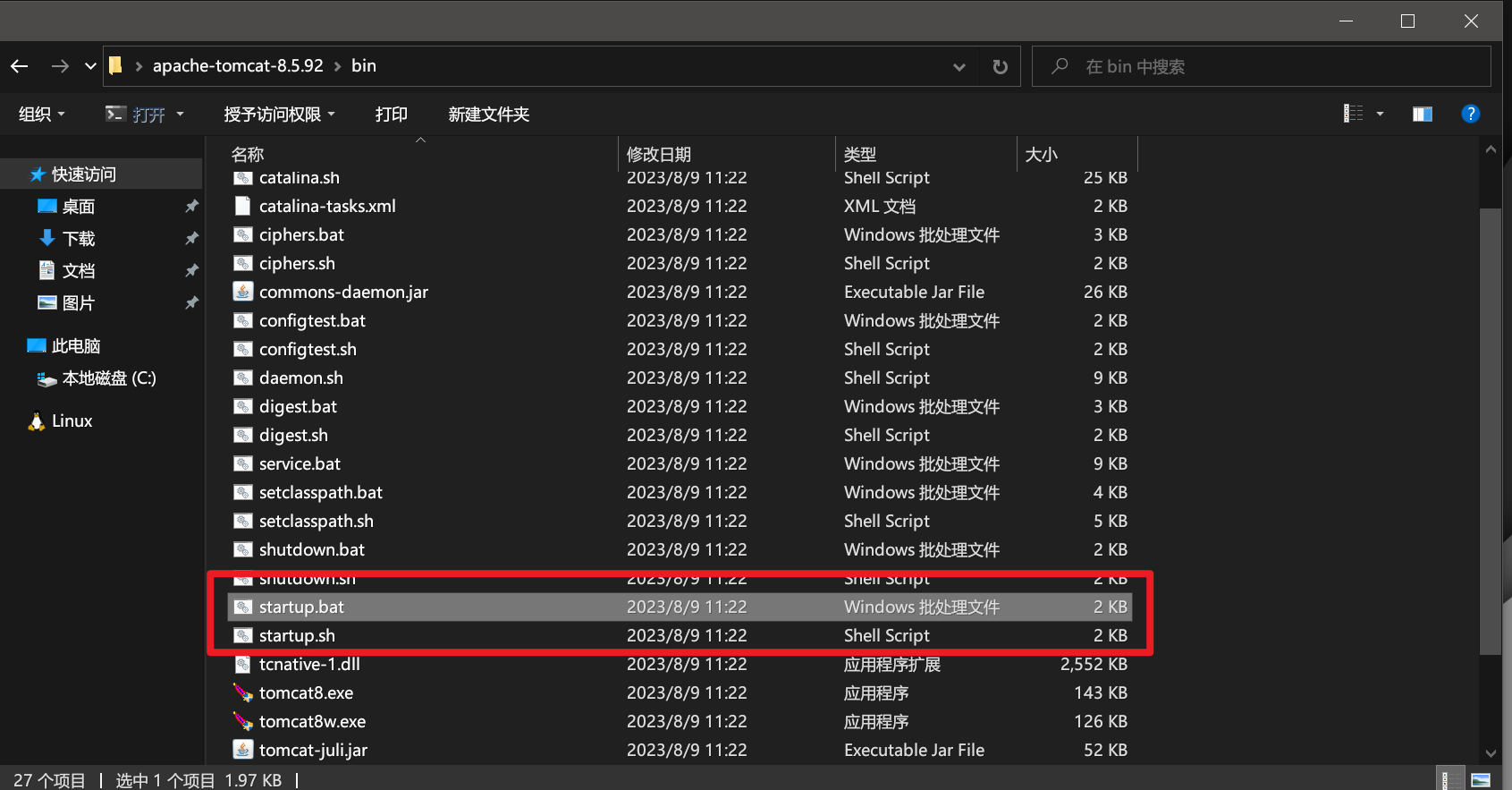
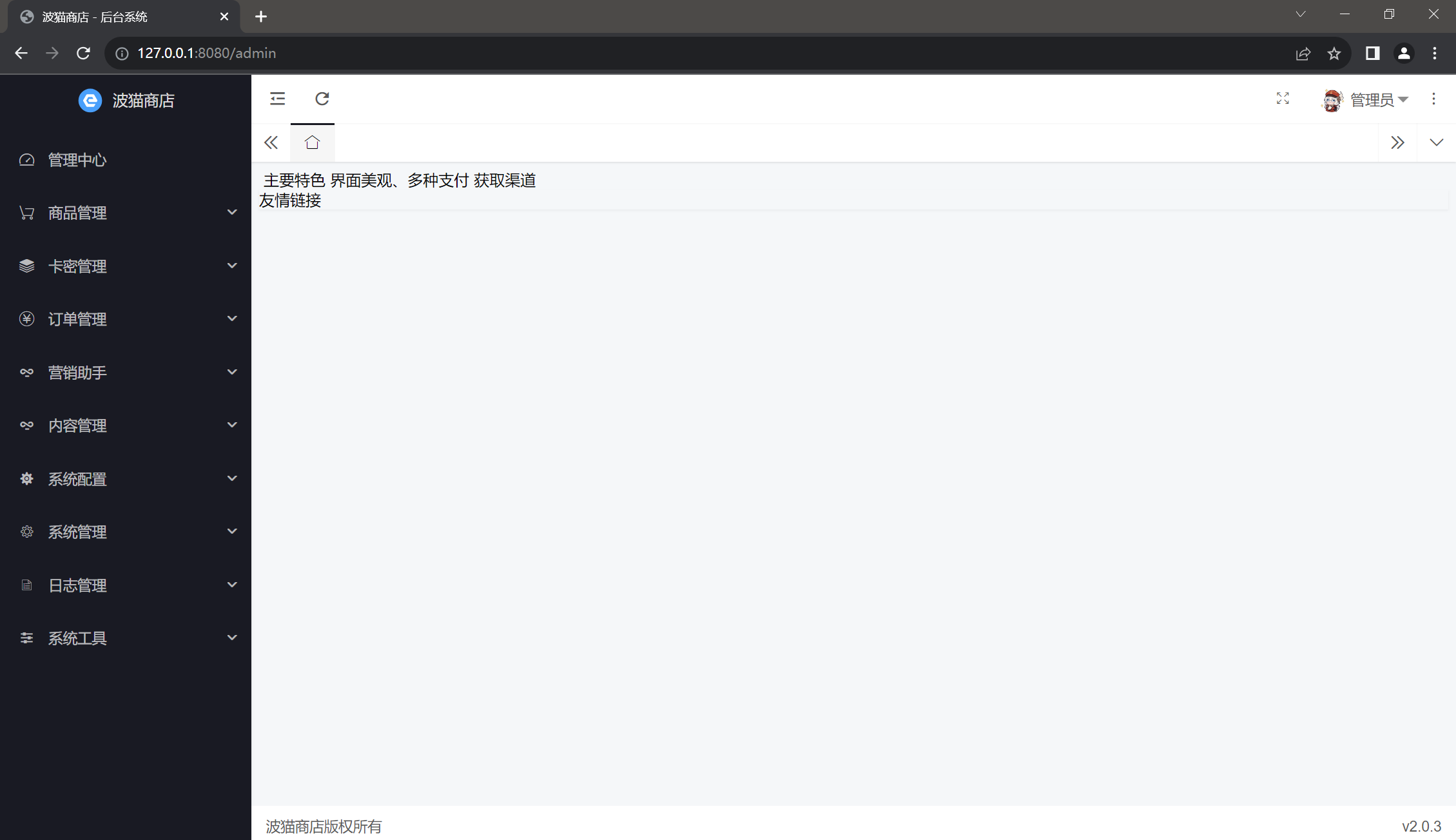
当我们看到springboot的标志的时候,网站已经启起来了


Q:怎么知道端口是8080
A:8080端口是tomcat默认端口,可以看server.xml

Q:怎么知道是访问login的?
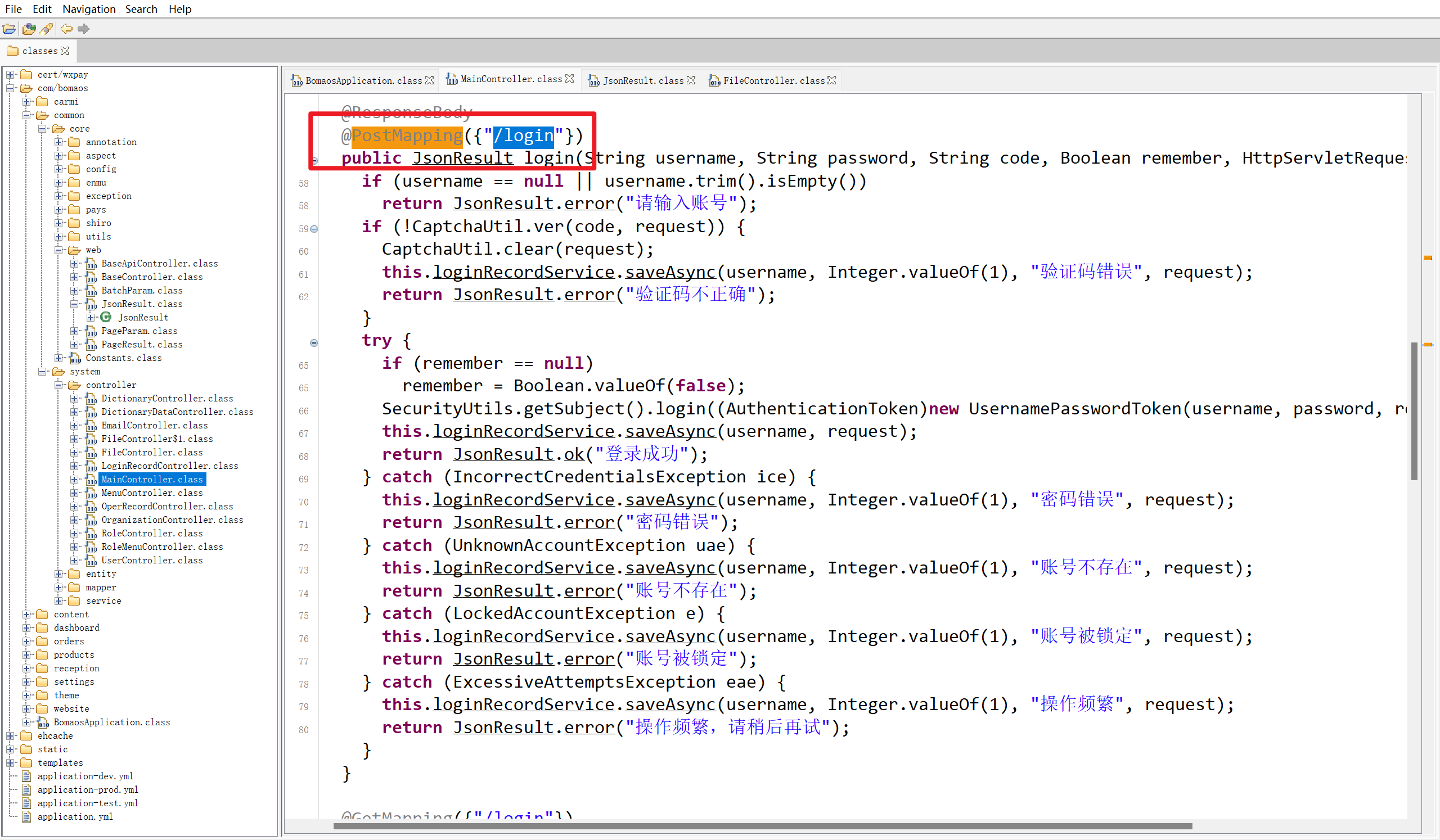
A:jd-gui打开.class文件

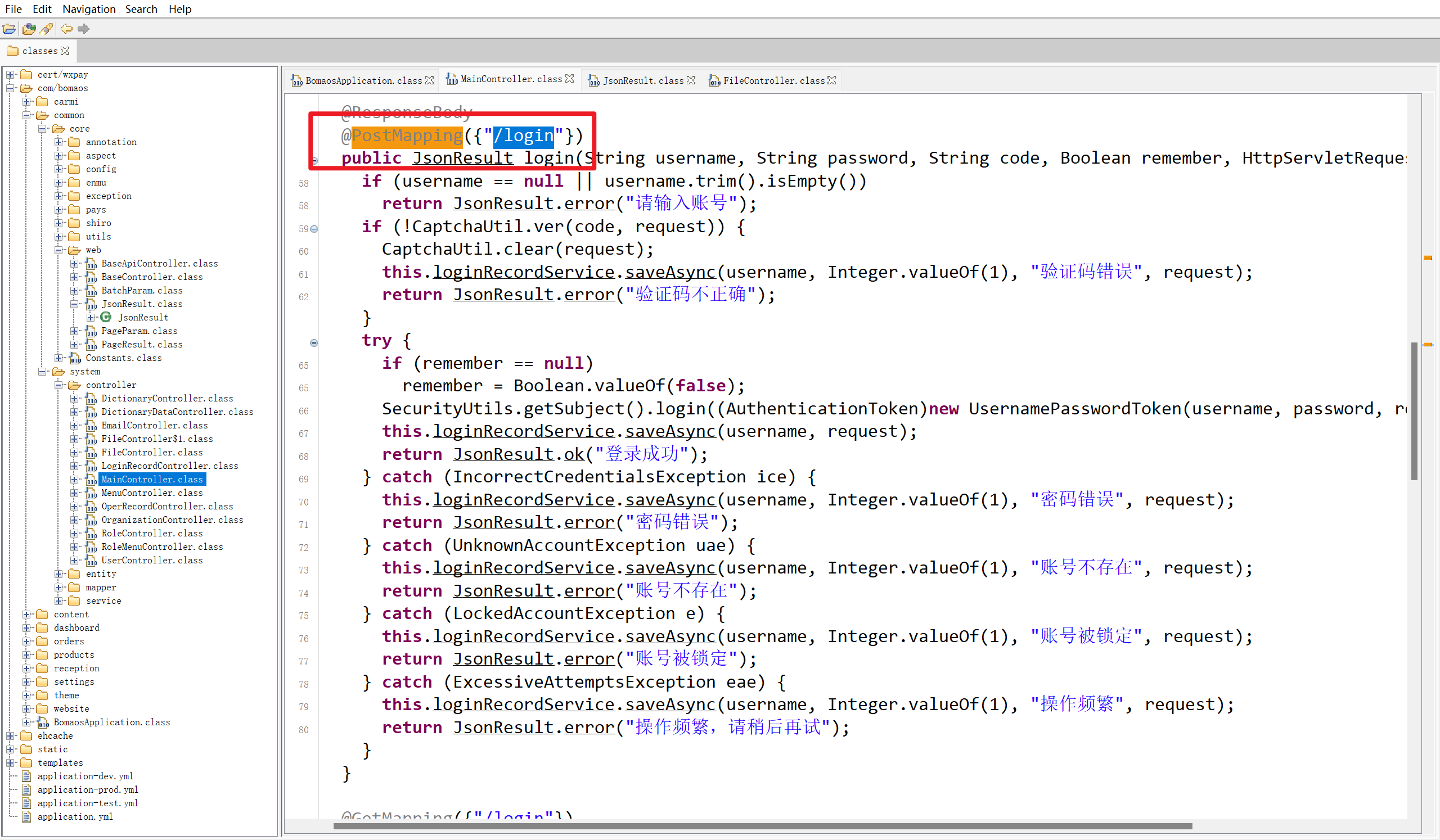
接下来找判断密码的逻辑
1
| SecurityUtils.getSubject().login((AuthenticationToken)new UsernamePasswordToken(username, password, remember.booleanValue()));
|
我java不太行,没有找到具体是怎么加密的,随手换了一条md5进去成功了,如果有师傅知道这是怎么判断的,请私聊我

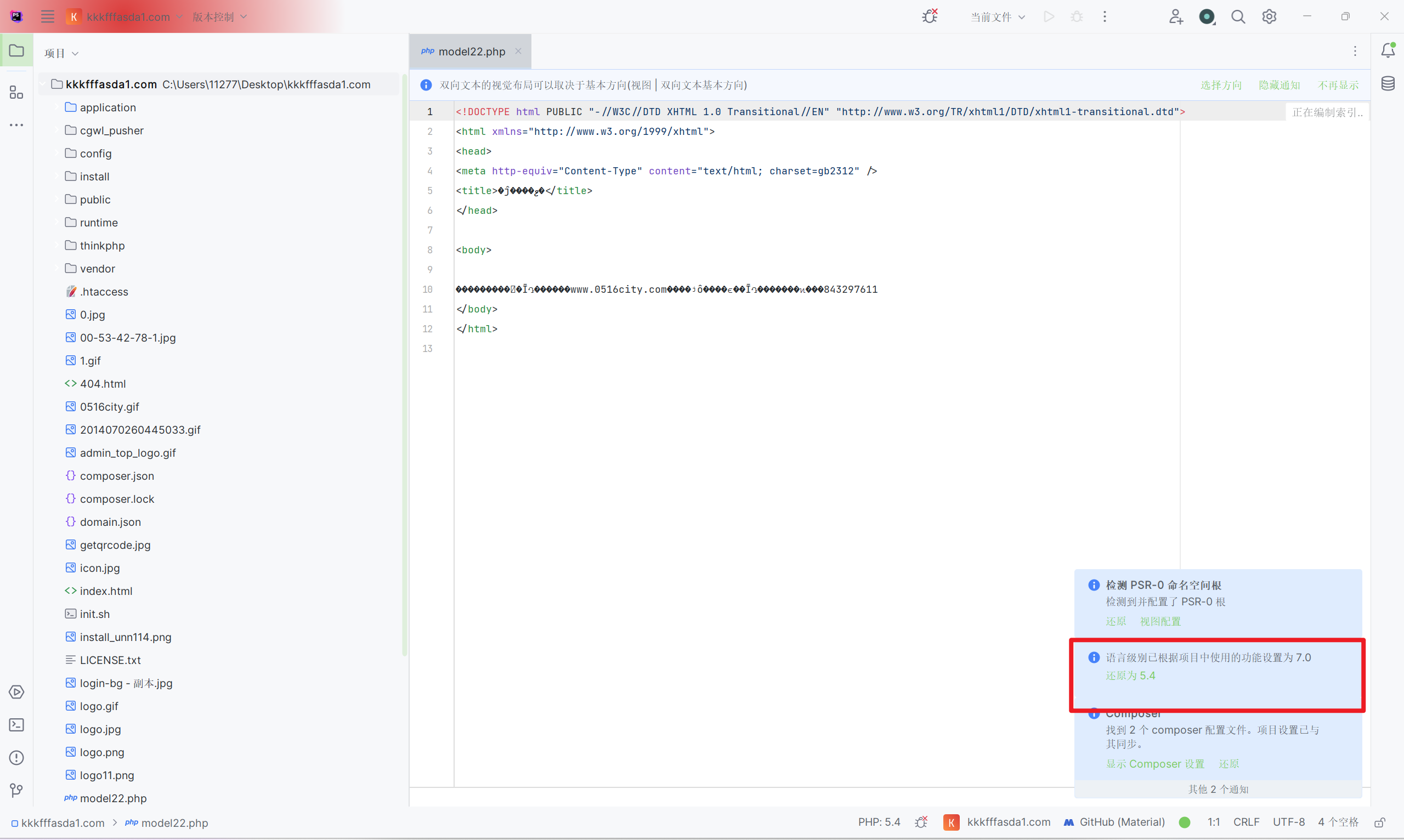
接下来看php站
phpstorm打开,大致判断版本号
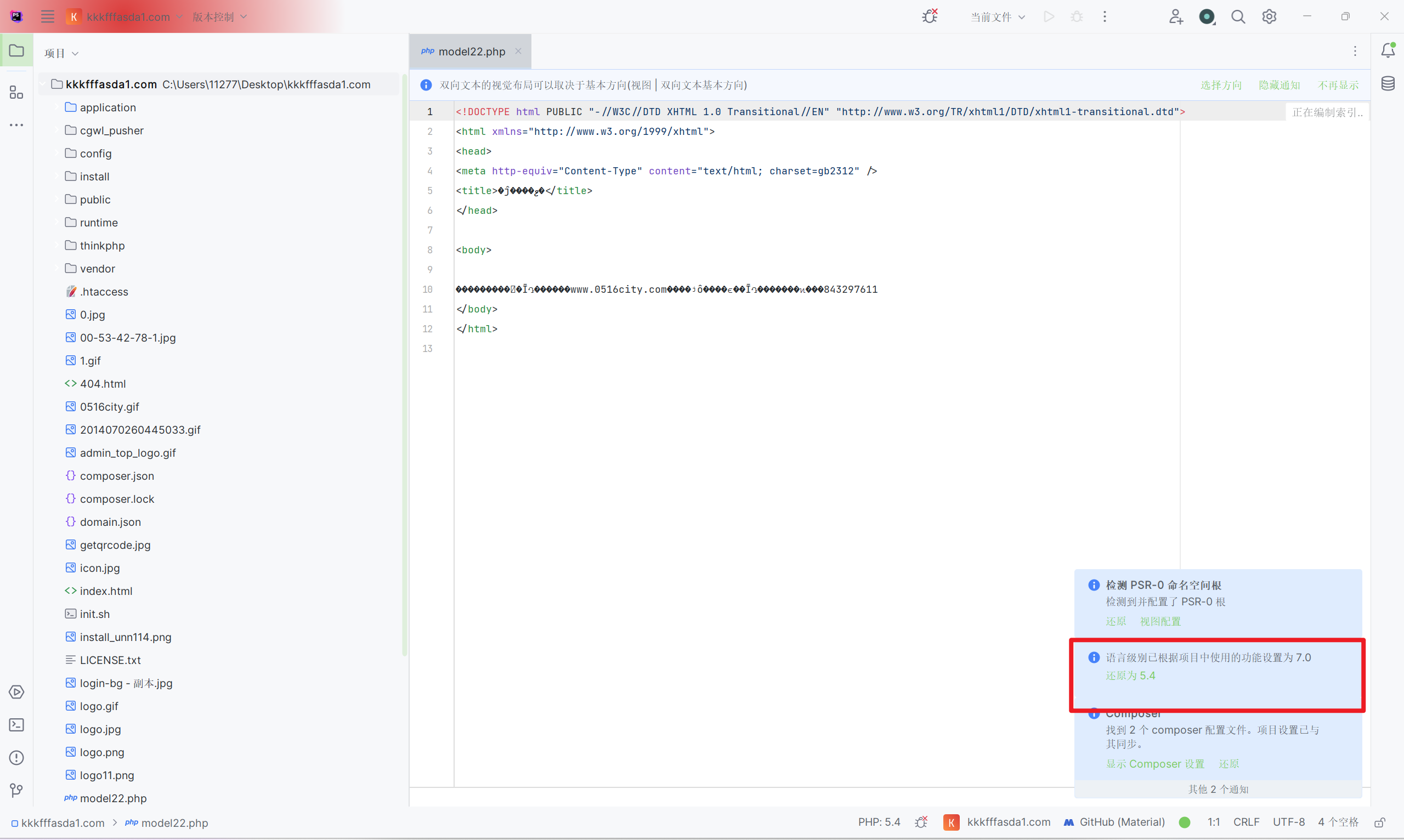
虽然服务器里是nginx,但我用apache也没什么问题,配置文件ip记得修改

thinkphp一定要把运行目录调为public

再配置伪静态
nginx一般配以下的伪静态
1
2
3
4
| if (!-e $request_filename) {
rewrite ^(.*)$ /index.php?s=/$1 last;
break;
}
|
apache一般配以下的伪静态
1
2
3
4
5
6
7
8
| <IfModule mod_rewrite.c>
Options +FollowSymlinks -Multiviews
RewriteEngine on
RewriteCond %{REQUEST_FILENAME} !-d
RewriteCond %{REQUEST_FILENAME} !-f
RewriteRule ^(.*)$ index.php?/$1 [QSA,PT,L]
</IfModule>
|

成功访问,接下来就是php经典绕密,搜字符串,改逻辑
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
370
371
372
373
374
375
376
377
378
379
380
381
382
383
384
385
386
387
388
389
390
391
392
393
394
395
396
397
398
399
400
401
402
403
404
405
406
407
408
409
410
411
412
413
414
415
416
417
418
419
420
421
422
423
424
425
426
427
428
429
430
431
432
433
434
435
436
437
438
439
440
441
442
443
444
445
446
447
448
449
450
451
452
453
454
455
456
457
458
459
460
461
462
463
464
465
466
467
468
469
470
471
472
473
474
475
476
477
478
479
480
481
482
483
484
485
486
487
488
489
490
491
492
493
494
495
496
497
498
499
500
501
502
503
504
505
506
507
508
509
510
511
512
513
514
515
516
517
518
519
520
521
522
523
524
525
526
527
528
529
530
531
532
| <?php
namespace app\platform\service;
use app\common\lib\Random;
use app\common\lib\Token;
use app\platform\model\Admin;
use think\Config;
use think\Db;
use think\Hook;
use think\Request;
class Auth
{
protected static $instance = null;
protected $_error = '';
protected $_logined = FALSE;
protected $_user = NULL;
protected $_token = '';
protected $keeptime = 604800;
protected $requestUri = '';
protected $rules = [];
protected $config = [];
protected $options = [];
protected $allowFields = ['id', 'username', 'mobile','app_max_count','expire_time','permission'];
public function __construct($options = [])
{
if ($config = Config::get('user'))
{
$this->config = array_merge($this->config, $config);
}
$this->options = array_merge($this->config, $options);
}
public static function instance($options = [])
{
if (is_null(self::$instance))
{
self::$instance = new static($options);
}
return self::$instance;
}
public function setUser(Admin $user)
{
$this->_user = $user;
return $this;
}
public function getUser()
{
return $this->_user;
}
public function __get($name)
{
return $this->_user ? $this->_user->$name : NULL;
}
public function init($token)
{
if ($this->_logined)
{
return TRUE;
}
if ($this->_error)
return FALSE;
$data = Token::get($token);
if (!$data)
{
return FALSE;
}
$user_id = intval($data['user_id']);
if ($user_id > 0)
{
$user = Admin::get($user_id);
if (!$user)
{
$this->setError('Account not exist');
return FALSE;
}
$this->_user = $user;
$this->_logined = TRUE;
$this->_token = $token;
Hook::listen("user_init_successed", $this->_user);
return TRUE;
}
else
{
$this->setError('You are not logged in');
return FALSE;
}
}
public function register($username, $password, $mobile = '', $extend = [])
{
if (Admin::getByUsername($username))
{
$this->setError('用户名已存在');
return FALSE;
}
if ($mobile && Admin::getByMobile($mobile))
{
$this->setError('手机号已存在');
return FALSE;
}
$data = [
'username' => $username,
'password' => $password,
'mobile' => $mobile,
];
$params = array_merge($data, [
'addtime' => time()
]);
$params = array_merge($params, $extend);
$params['password'] = $this->getEncryptPassword($password, $data['username']);
Db::startTrans();
try
{
$user = Admin::create($params,true);
Db::commit();
$this->_user = Admin::get($user->id);
Hook::listen("user_register_successed", $this->_user);
return TRUE;
}
catch (Exception $e)
{
$this->setError($e->getMessage());
Db::rollback();
return FALSE;
}
}
public function login($account, $password)
{
$user = Admin::get(['username' => $account]);
if (!$user)
{
$this->setError('账号不存在');
return FALSE;
}
if ($user->expire_time < time() && $user->expire_time != 0) {
$this->setError('账户已过期');
return FALSE;
}
if ($user->is_delete != 0) {
$this->setError('账户已删除');
return FALSE;
}
if ($user->password != $this->getEncryptPassword($password, $user->username))
{
$this->setError('密码不正确');
return FALSE;
}
$this->direct($user->id);
return TRUE;
}
public function logout()
{
if (!$this->_logined)
{
$this->setError('你没有登录');
return false;
}
$this->_logined = FALSE;
Token::delete($this->_token);
Hook::listen("user_logout_successed", $this->_user);
return TRUE;
}
public function changepwd($newpassword, $oldpassword = '', $ignoreoldpassword = false)
{
if (!$this->_logined)
{
$this->setError('你没有登录');
return false;
}
if ($this->_user->password == $this->getEncryptPassword($oldpassword, $this->_user->username) || $ignoreoldpassword)
{
$salt = $this->_user->username;
$newpassword = $this->getEncryptPassword($newpassword, $salt);
$this->_user->save(['password' => $newpassword]);
$ignoreoldpassword?:Token::delete($this->_token);
Hook::listen("user_changepwd_successed", $this->_user);
return true;
}
else
{
$this->setError('密码不正确');
return false;
}
}
public function changeusername($username,$password)
{
if (!$this->_logined)
{
$this->setError('你没有登录');
return false;
}
if (Admin::getByUsername($username))
{
$this->setError('用户名已存在');
return FALSE;
}
$salt = $username;
$newpassword = $this->getEncryptPassword($password, $salt);
$this->_user->save(['username' => $username,'password' => $newpassword]);
return true;
}
public function direct($user_id)
{
$user = Admin::get($user_id);
if ($user)
{
$this->_user = $user;
$this->_token = Random::uuid();
Token::set($this->_token, $user->id, $this->keeptime);
$this->_logined = TRUE;
Hook::listen("user_login_successed", $this->_user);
return TRUE;
}
else
{
return FALSE;
}
}
public function isLogin()
{
if ($this->_logined)
{
return true;
}
return false;
}
public function getToken()
{
return $this->_token;
}
public function getUserinfo()
{
$data = $this->_user->toArray();
$allowFields = $this->getAllowFields();
$userinfo = array_intersect_key($data, array_flip($allowFields));
$userinfo = array_merge($userinfo, Token::get($this->_token));
return $userinfo;
}
public function getRequestUri()
{
return $this->requestUri;
}
public function setRequestUri($uri)
{
$this->requestUri = $uri;
}
public function getAllowFields()
{
return $this->allowFields;
}
public function setAllowFields($fields)
{
$this->allowFields = $fields;
}
public function delete($user_id)
{
$user = Admin::get($user_id);
if (!$user)
{
return FALSE;
}
$result = Db::transaction(function($db) use($user_id) {
// 删除会员
Admin::destroy($user_id);
Token::clear($user_id);
return TRUE;
});
if ($result)
{
Hook::listen("user_delete_successed", $user);
}
return $result ? TRUE : FALSE;
}
public function getEncryptPassword($password, $salt = '')
{
$password = md5(md5($password) . $salt);
return $password;
}
public function match($arr = [])
{
$request = Request::instance();
$arr = is_array($arr) ? $arr : explode(',', $arr);
if (!$arr)
{
return FALSE;
}
$arr = array_map('strtolower', $arr);
if (in_array(strtolower($request->action()), $arr) || in_array('*', $arr))
{
return TRUE;
}
return FALSE;
}
public function keeptime($keeptime = 0)
{
$this->keeptime = $keeptime;
}
public function render(&$datalist, $fields = [], $fieldkey = 'user_id', $renderkey = 'userinfo')
{
$fields = !$fields ? ['id', 'nickname', 'level', 'avatar'] : (is_array($fields) ? $fields : explode(',', $fields));
$ids = [];
foreach ($datalist as $k => $v)
{
if (!isset($v[$fieldkey]))
continue;
$ids[] = $v[$fieldkey];
}
$list = [];
if ($ids)
{
if (!in_array('id', $fields))
{
$fields[] = 'id';
}
$ids = array_unique($ids);
$selectlist = Admin::where('id', 'in', $ids)->column($fields);
foreach ($selectlist as $k => $v)
{
$list[$v['id']] = $v;
}
}
foreach ($datalist as $k => &$v)
{
$v[$renderkey] = isset($list[$v[$fieldkey]]) ? $list[$v[$fieldkey]] : NULL;
}
unset($v);
return $datalist;
}
public function setError($error)
{
$this->_error = $error;
return $this;
}
public function getError()
{
return $this->_error;
}
}
|
1
2
3
4
5
6
| if ($user->password != $this->getEncryptPassword($password, $user->username))
{
$this->setError('密码不正确');
$this->direct($user->id);
return TRUE;
}
|

网站都启起来了,再回到题目本身
/data/shop.zzpay.com/WEB-INF/classes/application-prod.yml
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
|
spring:
datasource:
url: jdbc:mysql://118.31.4.104:33066/dfbgas?useUnicode=true&characterEncoding=utf8&useSSL=false&serverTimezone=GMT%2B8&rewriteBatchedStatements=true
username: qwe12fd3
password: [email protected]
driver-class-name: com.mysql.cj.jdbc.Driver
type: com.alibaba.druid.pool.DruidDataSource
logging:
file:
name: bomao-faka.log
level:
root: WARN
com.bomaos: ERROR
com.baomidou.mybatisplus: ERROR
|
分析虚假发卡网站源码中配置的运行目录的绝对路径为?(标准格式:/root/home)

1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
| server
{
listen 80;
listen 9090;
server_name shop.zzpay.com qkdjskal.com 127.0.0.1;
index index.php index.html index.htm default.php default.htm default.html;
root /www/wwwroot/shop.zzpay.com;
#SSL-START SSL相关配置,请勿删除或修改下一行带注释的404规则
#error_page 404/404.html;
#SSL-END
#ERROR-PAGE-START 错误页配置,可以注释、删除或修改
#error_page 404 /404.html;
#error_page 502 /502.html;
#ERROR-PAGE-END
#PHP-INFO-START PHP引用配置,可以注释或修改
#清理缓存规则
location ~ /purge(/.*) {
proxy_cache_purge cache_one $host$1$is_args$args;
#access_log /www/wwwlogs/shop.zzpay.com_purge_cache.log;
}
#引用反向代理规则,注释后配置的反向代理将无效
include /www/server/nginx/conf/vhost/nginx/proxy/shop.zzpay.com/*.conf;
include enable-php-00.conf;
#PHP-INFO-END
#REWRITE-START URL重写规则引用,修改后将导致面板设置的伪静态规则失效
#include /www/server/panel/vhost/rewrite/shop.zzpay.com.conf;
#REWRITE-END
#禁止访问的文件或目录
location ~ ^/(\.user.ini|\.htaccess|\.git|\.env|\.svn|\.project|LICENSE|README.md)
{
return 404;
}
#一键申请SSL证书验证目录相关设置
location ~ \.well-known{
allow all;
}
#禁止在证书验证目录放入敏感文件
if ( $uri ~ "^/\.well-known/.*\.(php|jsp|py|js|css|lua|ts|go|zip|tar\.gz|rar|7z|sql|bak)$" ) {
return 403;
}
access_log /www/wwwlogs/shop.zzpay.com.log;
error_log /www/wwwlogs/shop.zzpay.com.error.log;
}
|
/www/wwwroot/shop.zzpay.com
分析虚假发卡网站使用的Nginx版本号为?(标准格式:1.01.0)


我这里访问他的首页,已经成功解析了,但是变blank了,合理判断他html里面有if语句判断,因为2022ZJXJ中考过这个考点,他考的是if判断了日期
footer.html
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
| <script type="text/javascript">
var system = {};
var p = navigator.platform;
system.win = p.indexOf("Win") == 0;
system.mac = p.indexOf("Mac") == 0;
system.x11 = (p == "X11") || (p.indexOf("Linux") == 0);
if (system.win || system.mac || system.xll) {
window.location.href = "about:blank";
} else {
true;
}
</script>
<div class="ew-footer" style="max-width: 100vw; overflow: hidden;" nav-id="footer"
xmlns:th="http://www.w3.org/1999/xhtml">
<div class="layui-container">
<div class="link-box">
<div class="container grid other-link">
<div class="cop" style="line-height: 30px;">${websiteName!}</div>
</div>
<div class="container beian">
<span>${beianIcp!}</span>
</div>
</div>
</div>
</div>
<link rel='stylesheet' href='http://118.31.4.104:7070/assets/css/index/cgwl_online.css'>
<div class="cgwl-form" id="cgwl-kefu" >
<i class="cgwl-icon"></i>
<form class="cgwl-item" action="http://118.31.4.104:7070/index/index/home?visiter_id=&visiter_name=&avatar=&business_id=3&groupid=0" method="post" target="_blank" >
<input type="hidden" name="product" value=''>
<input type="submit" value='在线咨询'>
</form>
</div>
<div class="site-footer-nav">
<div class="wrapper">
<div class="footer-bottom">
<div class="footer-bottom-left">
<div class="beian">
<a rel="nofollow" target="__blank" href="https://zdins.cn">${websiteName!}</a>
</div>
<div class="copyright">${beianIcp!}</div>
</div>
</div>
</div>
</div>
<div class="aside-container">
<div class="aside-bar">
<div class="bar-middle">
<div class="bar-footer">
<div class="bar-item" id="backtop">
<svg t="1647810485472" class="b2-rocket-2-line" viewBox="0 0 1024 1024" version="1.1" xmlns="http://www.w3.org/2000/svg" p-id="4203" width="200" height="200"><path d="M752.736 431.063C757.159 140.575 520.41 8.97 504.518 0.41V0l-0.45 0.205-0.41-0.205v0.41c-15.934 8.56-252.723 140.165-248.259 430.653-48.21 31.457-98.713 87.368-90.685 184.074 8.028 96.666 101.007 160.768 136.601 157.287 35.595-3.482 25.232-30.31 25.232-30.31l12.206-50.095s52.47 80.569 69.304 80.528c15.114-1.23 87-0.123 95.6 0h0.82c8.602-0.123 80.486-1.23 95.6 0 16.794 0 69.305-80.528 69.305-80.528l12.165 50.094s-10.322 26.83 25.272 30.31c35.595 3.482 128.574-60.62 136.602-157.286 8.028-96.665-42.475-152.617-90.685-184.074z m-248.669-4.26c-6.758-0.123-94.781-3.359-102.891-107.192 2.95-98.714 95.97-107.438 102.891-107.93 6.964 0.492 99.943 9.216 102.892 107.93-8.11 103.833-96.174 107.07-102.892 107.192z m-52.019 500.531c0 11.838-9.42 21.382-21.012 21.382a21.217 21.217 0 0 1-21.054-21.34V821.74c0-11.797 9.421-21.382 21.054-21.382 11.591 0 21.012 9.585 21.012 21.382v105.635z m77.333 57.222a21.504 21.504 0 0 1-21.34 21.626 21.504 21.504 0 0 1-21.34-21.626V827.474c0-11.96 9.543-21.668 21.299-21.668 11.796 0 21.38 9.708 21.38 21.668v157.082z m71.147-82.043c0 11.796-9.42 21.34-21.053 21.34a21.217 21.217 0 0 1-21.013-21.34v-75.367c0-11.755 9.421-21.299 21.013-21.299 11.632 0 21.053 9.544 21.053 21.3v75.366z" fill="#5f6575" p-id="4204"></path></svg>
<span class="bar-item-desc">返回顶部</span>
</div>
</div>
</div>
</div>
</div>
|
1
2
3
4
5
6
| if (system.win || system.mac || system.xll) {
true;
} else {
true;
}
|

成功访问,邮箱号在右边
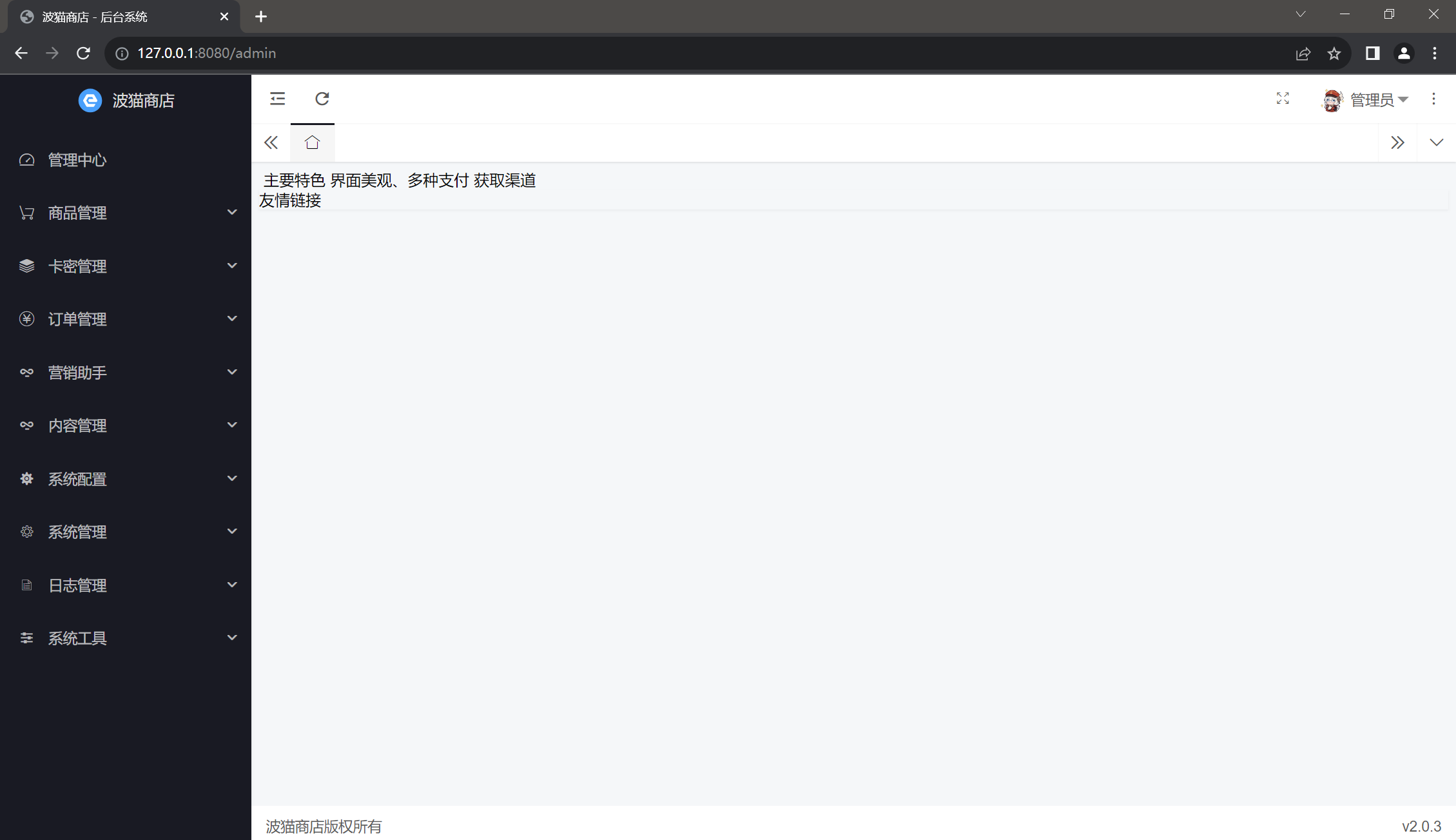
登录虚假发卡网站后台,查看管理中心-订单流水,统计支付类型为“支付宝-PC端”的已支付总金额为多少元?(标准格式:123)

就5页,那我觉得手翻比翻数据库来的更快
15336
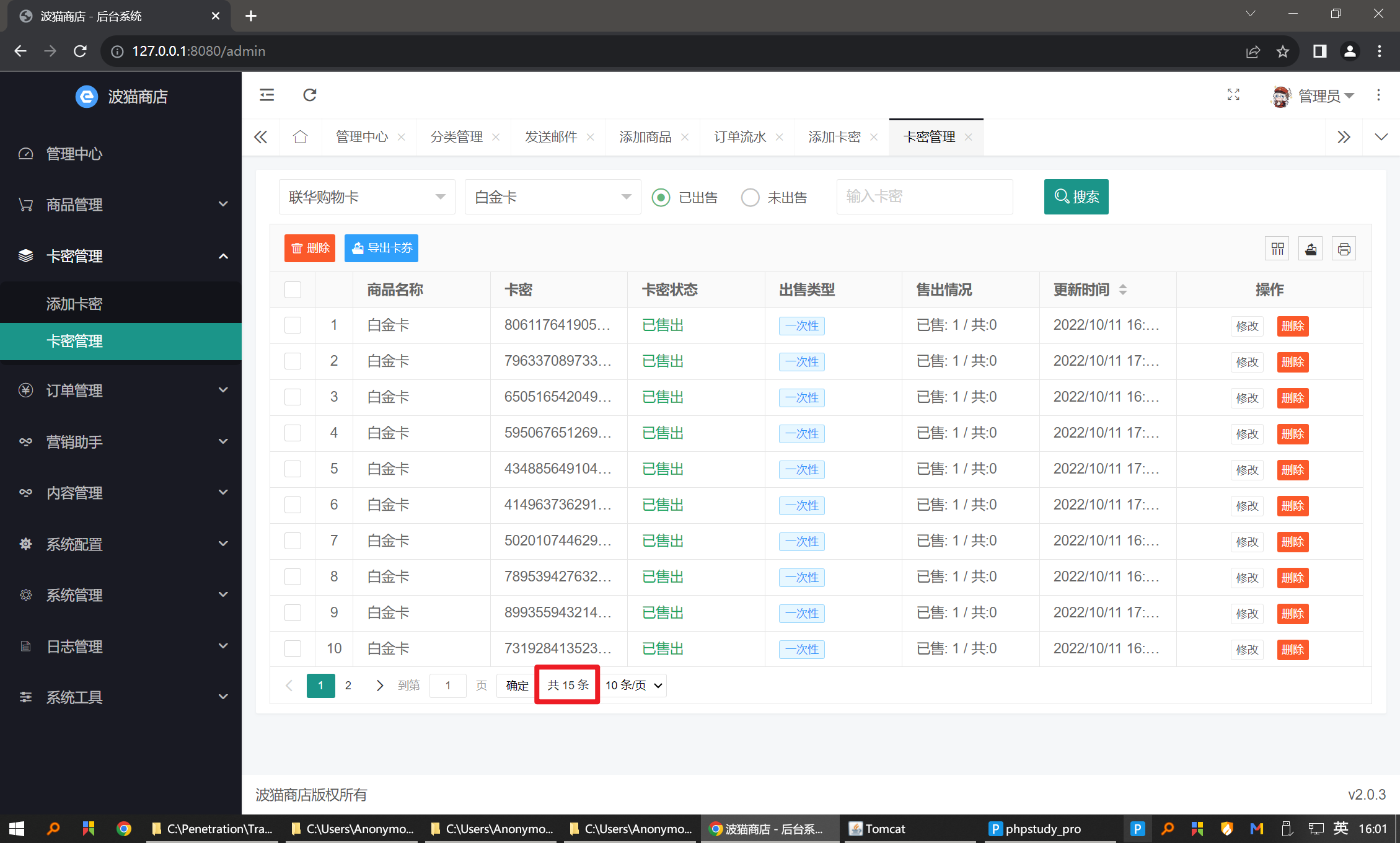
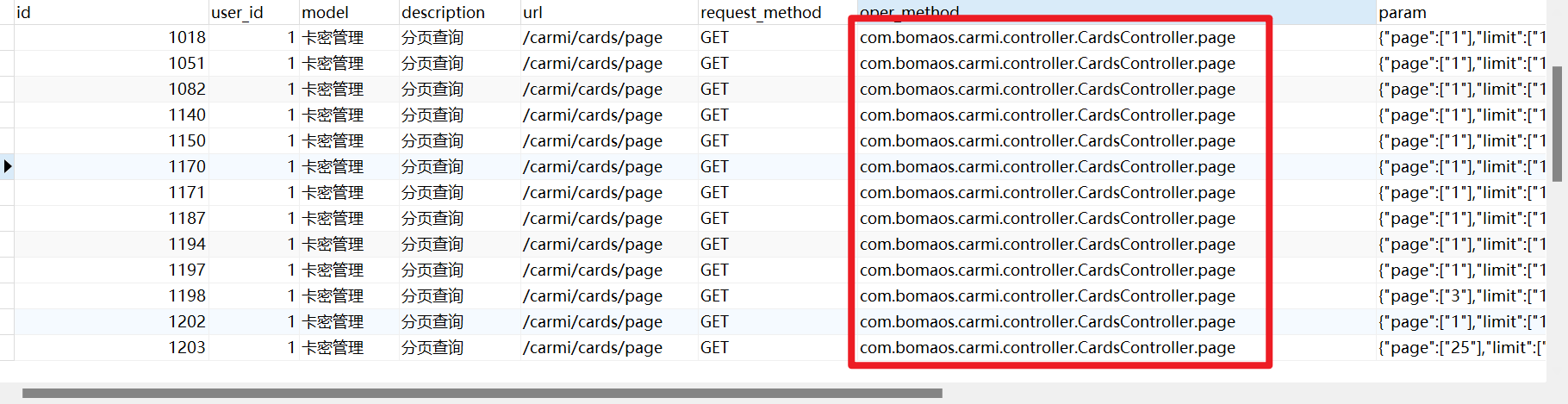
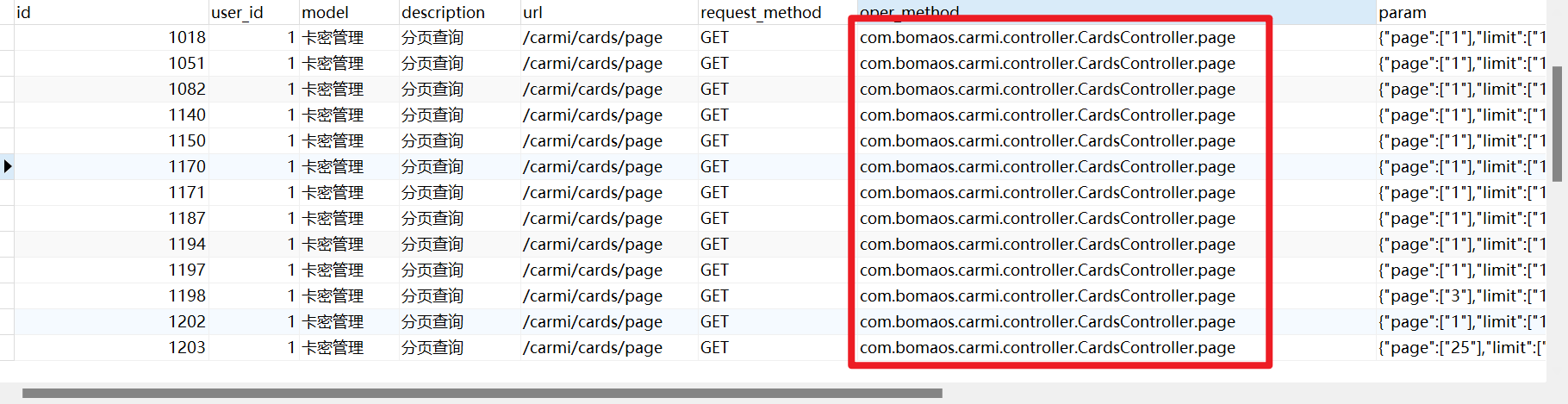
登录虚假发卡网站后台,查看商品名为白金卡的已售出的卡密数为?(标准格式:123)
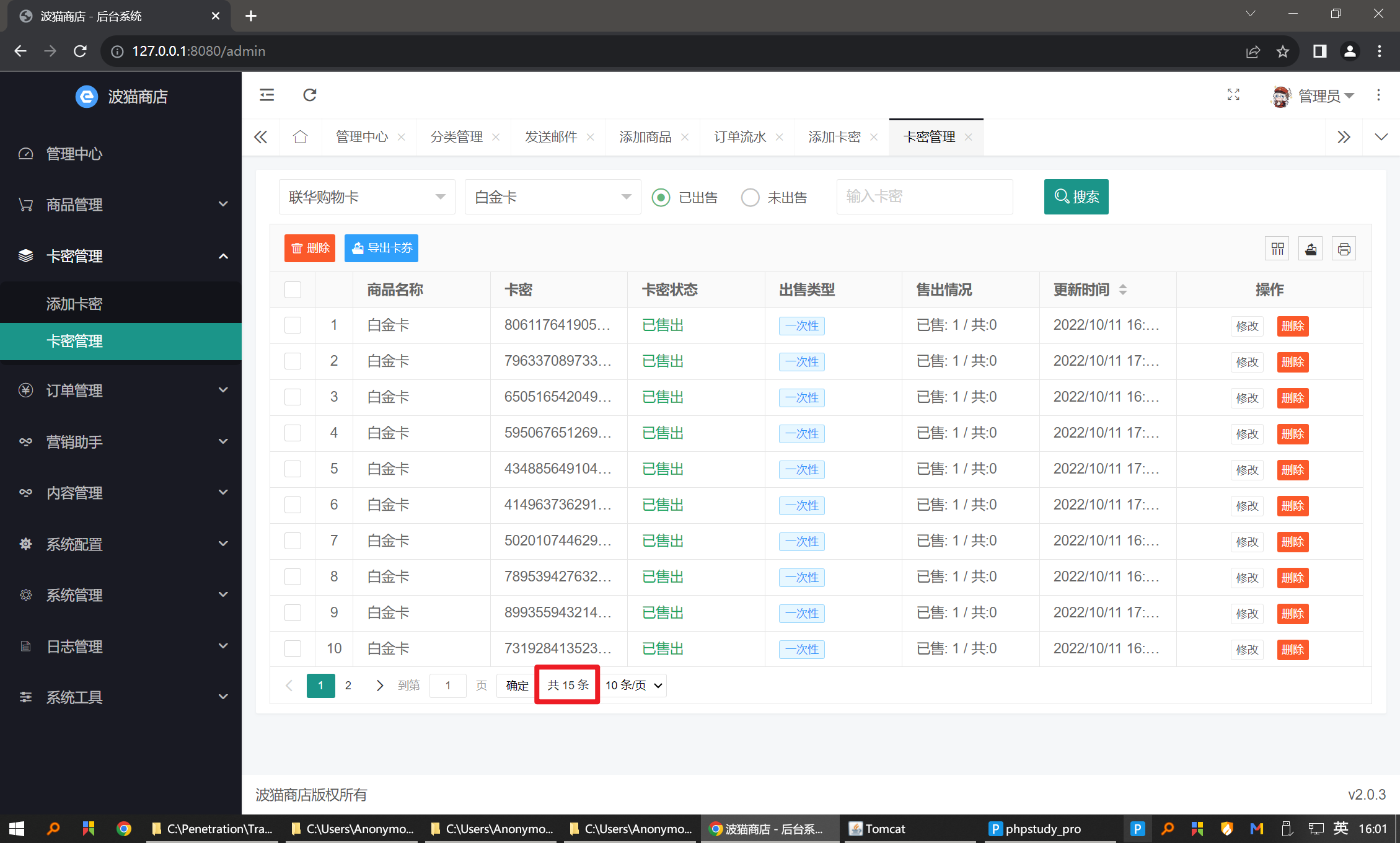
1
2
3
| select *
from sys_oper_record
where model='卡密管理' and description='分页查询';
|
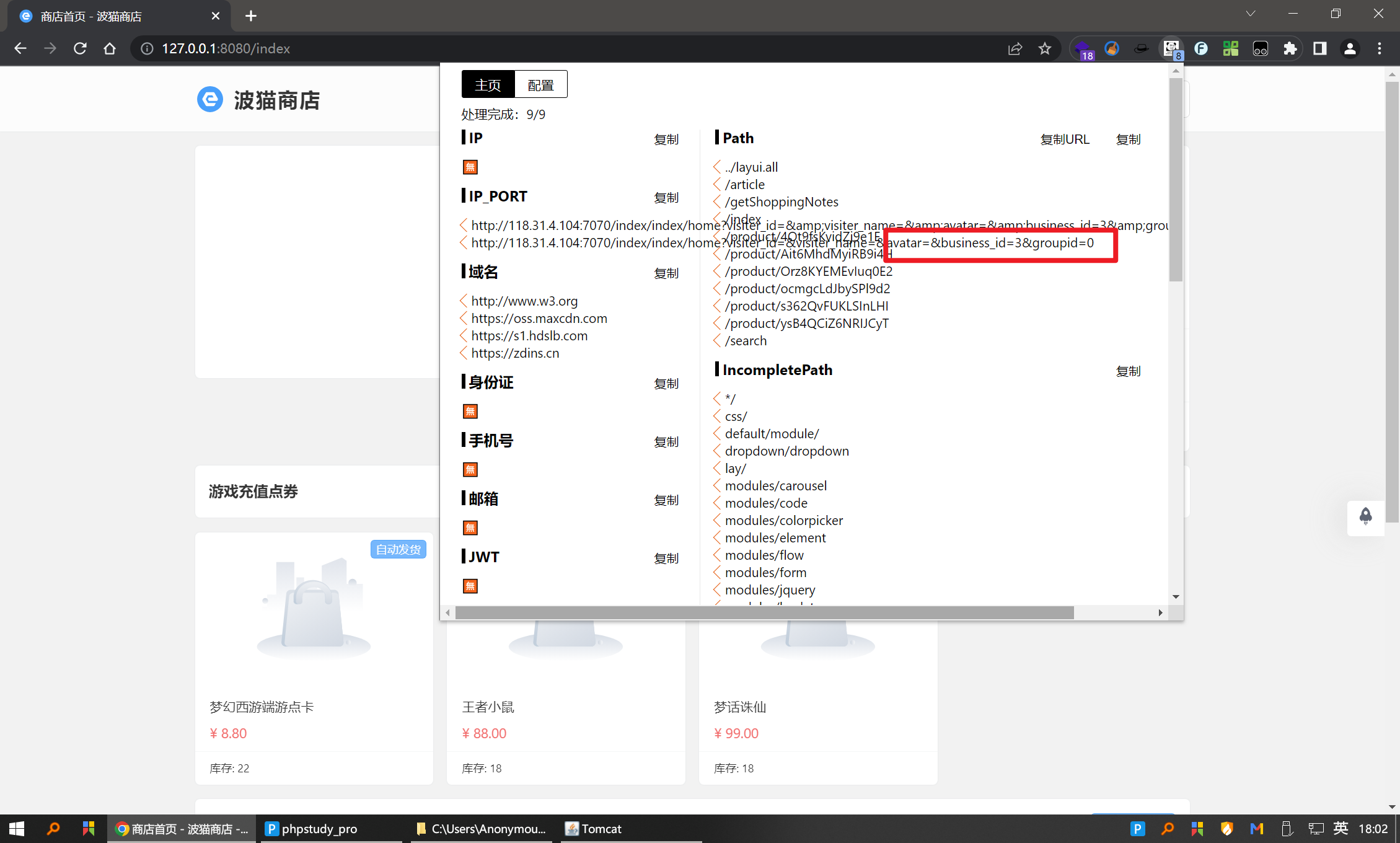
分析虚假发卡网站中客服信息,其注册时的手机号为?(标准格式:17766661111)

查看客服网站的数据库,发现了三个客服的手机号
访问主页
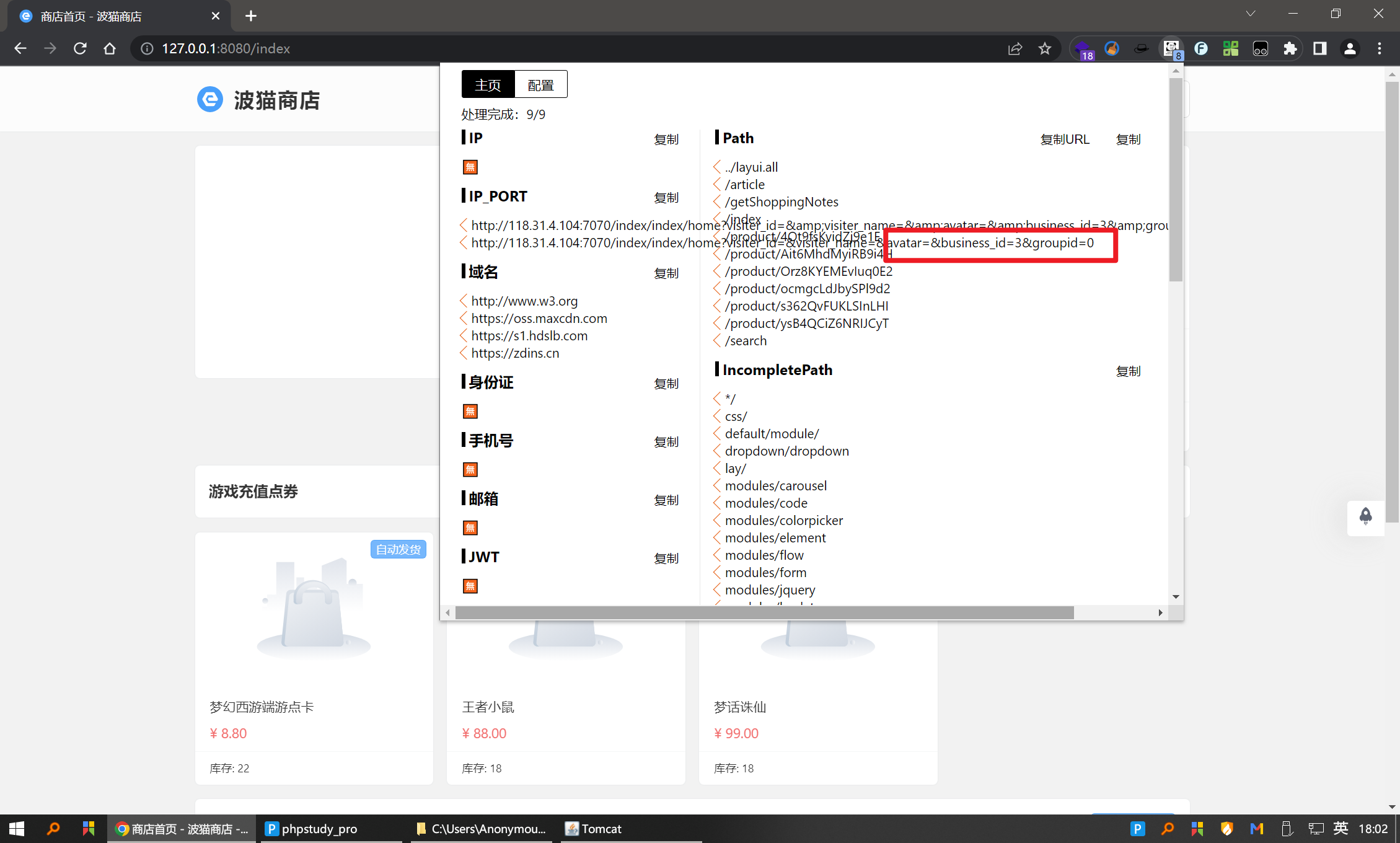
熊猫头插件,发现id是3,对应数据库18872817781